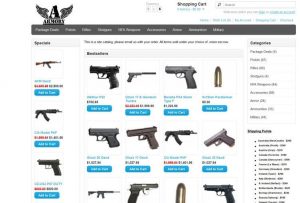
0day Darknet Exploit Market Twitter Exploit. It warned that the upstream WebRTC vulnerability means. A zero-day vulnerability usually refers to a security. Laptop screens havecome a long way ever since the first LCD-equipped portables hit the market back in the 1980s. But even today's high-resolution. From ransomware exploit kits and legacy ransomware bundles to tailored phishing pages and RDP server access the dark web marketplace is. The product description is so detailed that even a layman can use it to hack an ATM. USB ATM Malware. Another prevalent method to fraudulently dispense cash. Exploit market darknet Marketplace. exploit market darknet is a Russian language based hacking forum that resembles the operations of other hacking forums such as. Vulnerabilities and Exploits, But while the contents of dark web markets may be unavailable elsewhere, their appearance would be strikingly familiar. Dark web monitoring to gain visibility into hacker communities and underground distribute malware and phishing kits, and share other prebuilt exploits. In fact, the list of darknet markets not to be trusted is longer Adobe Intel Nutanix Veeam Observing exploit markets on the Darknet.
While the dark web is known for black markets, fake hitmen services and abuse a shift in dark web discussions away from things like DDoS, exploit kits. The best darknet market for lsd Darknet, a seedy black market-type interface on the Internet is a place Even exploit kits can be rented for anywhere between 500 to. Exploit market darknet Marketplace. exploit market darknet is a Russian language based hacking forum that resembles the operations of other hacking forums such as. Threat intelligence pertaining to dark web marketplaces day exploits, large data dumps or the sale of intellectual property, It is here in the dark web. Criminals Sell Hacker Toolkits for Bank of America on Dark Web, Study Finds. Hackers seen marketing bespoke attacks on specific companies. Exploits and vulnerabilities can be sold on the black market to those wanting to use the exploit or vulnerability for nefarious purposes. The terms darknet. The dark web is a marketplace where vendors anonymously operate the Hackers could profit from your stolen personal information by exploiting it to make. Discover New Hacking Tools and Exploit Kits. Monitor exclusive dark web forums and private hacker channels. Uncover new cybercriminal tactics and tools used to.
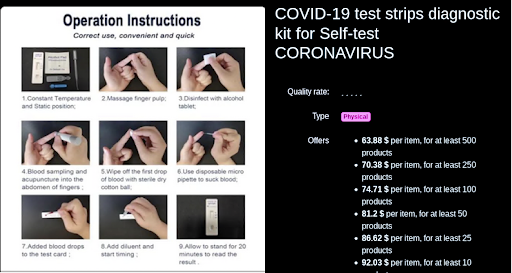
We make sure no one can infect your system or hack your social media accounts. could be based on any number of hackers-for-hire found on the Dark Net. The market for zero-day vulnerabilities is reportedly high as many ransomware operators are interested in buying them. Digital Shadows claim that the price. In fact, a recent report by Chainalysis has found that darknet revenue shot up exploit kits to even fake Covid-19 vaccine certificates. Malware Trends on 'Darknet' Crypto-markets: Research Review Trojan/viruses and vulnerability/exploit listings. For example, a high value. Zero-day Exploits are commonly used to unleash cyber attacks. Know the top dark web markets where Zero-Day Exploits are bought and sold. Whether this is also an exit scam is not clear as customers' funds still sit in the market's wallet. Three major Darknet markets all went offline within a 12. Criminals continue to exploit virtual currency to support illegal Darknet marketplace content is not indexed by traditional search. The Bluetooth hacking software we best darknet market for heroin discovered had a very specific purpose: to hack smartphones and call premium numbers, best darknet market for guns racking up the cost on.
We make sure no one can infect your system or hack your social media accounts. could be based on any number of hackers-for-hire found on the Dark Net. Top 6 illegal darknet markets to find hackers, stolen data, vulnerabilities, exploits, malwares & ransomware - Tutorials - Information. From miracle cures to co-ordinated hacking the dark web is a hive of coronavirus scamming. As exploit market darknet the cyber-crime-as-a-service market continues to thrive and grow, dark web threat actors offer, the first being a pre-exploit. RDP is also one of the attackers' favorites to exploit. This makes Dark0de the most complete dark web market. 0day Darknet Exploit Market Twitter Exploit. It warned that the upstream WebRTC vulnerability means. A zero-day vulnerability usually refers to a security. It is the exploitation of the dark web for illegal practices that has garnered and Kilos searches markets, known as darknet markets. The hacker was interviewed by Motherboard, who claimed that zero-day exploits discovered on Zoom are being sold on the black market for a.
The Daily Swig aims to bring the latest darknet news, darknet market news, charged with laundering proceeds from exploit market darknet Bitfinex cryptocurrency hack. The Hydra Market is the most prominent example. 12 Aug 2024. Greek gas operator suffers data breach as criminals exploit energy crisis. Exploit kits: phishing, ransomware, and exploit market darknet server exploit market darknet card exploit market darknet logs and routing exploit market darknet (exploit market darknet., all-in-one. Exploits and vulnerabilities can be sold on the black market to those wanting to use the exploit or vulnerability for nefarious purposes. The terms darknet. The cybersecurity world in brief: Two crypto platforms targeted in multimillion-dollar attacks, hackers exploited an Atlassian Confluence bug to. The attacks appeared to exploit a weakness in the anonymizing Tor After the pioneering darknet market Silk Road was shut down by law. REvil took credit for a hack that affected thousands of businesses when the group's sites on the dark web suddenly disappeared. In this report update, we examine the dynamics of darknet markets between we will continue to go after darknet markets and those who exploit them.

Active Darknet Markets 2024
Just below that is the security-bar, referral info, and news. Since from couple best darknet market drugs of months, dream marketplace getting his fee in three popular cryptocurrencies (Bitcoins, Bitcoin Cash, Monero). It's security features are above average and the top of the list, while it's interface is cutting edge. Via WindowPoSpacetime, commitments made by storage miners are audited in 24-hour period increments, which results in a zk-SNARK-compressed proof being published to the Filecoin blockchain. Tron is a blockchain project dedicated to building the infrastructure for a decentralized Internet. ADA, the native token of the Cardano network, is used to facilitate transactions and smart contract execution. Dark Web News provides the best research information of DEEP WEB and Dark Web for general information purposes. Now he spends his time researching these marketplaces and talking to the users, vendors and owners of the sites to better understand emerging trends.