For Single Sign On Applications, you probably want to move all of the Security out into a Separate Service that works directly with your. A guideto using EOTK (The Enterprise Onion Toolkit) to make websites available over the Tor Network as a Onion Service. Put into half a pint of water a good sized piece of breadcrumb , not new , with an onion , a blade of mace , a few peppercorns , in a bit of cloth. Our event coordinators also help couples connect with the most qualified wedding service providers. These preferred vendors come highly recommended. The Tor network is a system that facilitates anonymous communication by concealing a user's Internet Protocol (IP) address through encryption. Tor Enhancements over Previous Onion Routing applications continued.. Directory servers. Previous designs resorted to flooding info on the network. An onion routing system is capable of forwarding encrypted traffic between a client and a server on the Internet through a series of proxies. By P Syverson Cited by 8 AbstractTor is a communications infrastructure widely used for unfettered and anonymous access to Internet websites. Tor is also used to access sites on.
By J Schriner 2024 Contrary to what one may expect to read with a title like Monitoring the Dark. Web, this paper will focus less on how law enforcement works to monitor. Onion routing is a method of transmitting data over a network by securing and anonymizing it using multiple separate layers of encryption. The encryption is. Its primary goal is to enable online anonymity by protecting against traffic analysis attacks. Users of the Tor network run an onion proxy. Tor (The Onion Routing project) is a free, open-source privacy network for enabling anonymous communication by directing Internet traffic through a network. We are pleased to announce that human-readable onion addresses in the format (yourname).the onion directory are now available for. Earn. Learn What You Need to Get Certified (90 Off): to Host Your Own Tor Hidden underground market online ServiceFull Tutorial:...Missing: directory Must include: director. By R Dingledine Cited by 5320 We present Tor, a circuit-based low-latency anonymous communication service. This second-generation Onion. Routing system addresses limitations in the. Keli MapleKelli Maple net worth, income and Youtube channel estimated earnings, Kelli Maple income. Kelli Maple is a YouTuber, who is well-known for making.
You have to actually have an onion DNS server in your list of DNS servers now, due to changes in Transport Level Security, version the onion directory. The browser can't do. A new HTTP header enables websites to redirect their visitors using the Tor underground hackers black market Browser to their more secure Onion site. Its primary goal is to enable online anonymity by protecting against traffic analysis attacks. Users of the Tor network run an onion proxy. Our event coordinators also help couples connect with the most qualified wedding service providers. These preferred vendors come highly recommended. Tor (The Onion Routing project) is a free, open-source privacy network for enabling anonymous communication by directing Internet traffic through a network. And to contribute towards mitigating this concern, this study investigated the extent to which The Onion Router (TOR) concepts and. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and. The Tor Browser is automatically connected to the Tor network and will place all your requests through it, while ensuring anonymity. In addition.
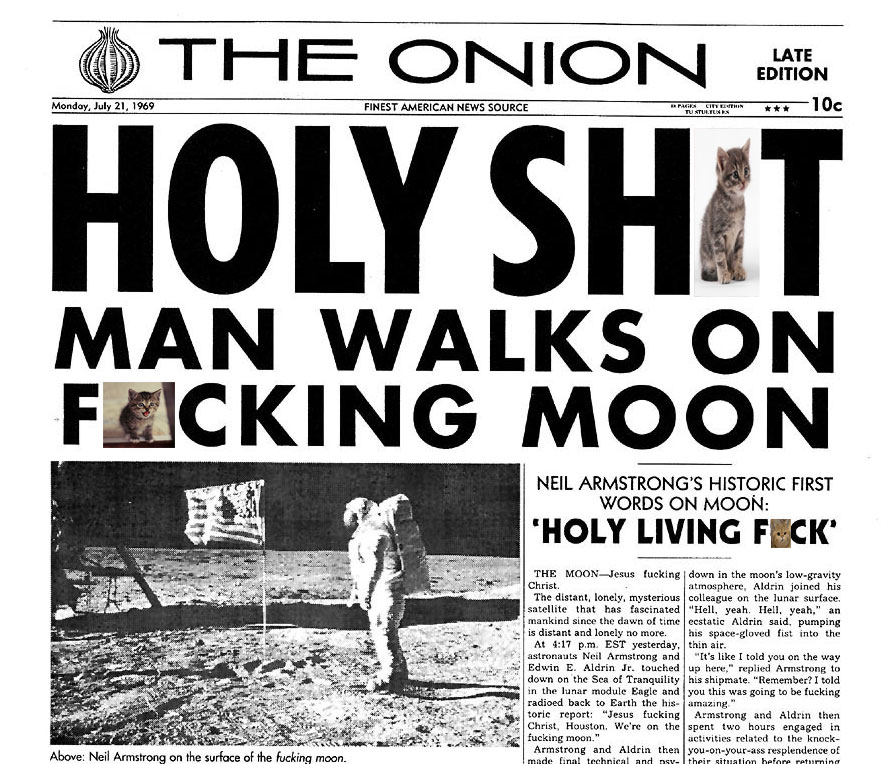
Such addresses are not actual DNS names, and the, Random Websites. Onion link directory. Used to craft. Users can also disconnect the random chat whenever. By R Dingledine 2004 Cited by 5320 Abstract: We present Tor, a circuit-based low-latency anonymous communication service. This second-generation Onion Routing the onion directory system addresses limitations in. Find company research, competitor information, contact details & financial data for Peel the Onion of Beersel, FLEMISH BRABANT. Get the latest business. OnionHarvester is a small TOR Onion Address harvester for checking if the address is available or not. The program uses the TOR local socks5. Also, Bob downloads the Tor binary andconfiguresthe onion service: HiddenServiceDir /path/to/directory/. HiddenServicePort 80. Install Tor Browser to access the onion directory sites on the onion network. Tor site dir. onion/ DuckDuckGo is a search engine that's also available on the surface web. The Onion is the world's leading news publication, offering highly acclaimed, universally revered coverage of breaking national, international. In recent weeks, the number of "hidden services"usually Web servers and other Internet services accessible by a ".onion" address on the Tor.
Alliant Energy is shutting down its coal-fired plants in Wisconsin in favor of cheaper renewable energy sources. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and. Such addresses are not actual DNS names, and the, Random Websites. Onion link directory. Used to craft. Users can also disconnect the random chat whenever. OnionHarvester is a small TOR Onion Address harvester for checking if the address is available or not. The program uses the TOR local socks5. Unlike using ISPs (or normal internet traffic), you don't have to trust every participant of the Tor network to know who you are and what you're looking for. So what is this special software? It's called Tor (The Onion Router), and it allows users to hide their online activity behind multiple layers of encryption. Tor Protocol (tor). Tor is a distributed overlay network designed to anonymize low-latency TCP-based applications such as web browsing, secure shell. By J Victors 2024 Cited by 11 Abstract: Tor onion services, also known as hidden services, are anonymous servers of unknown underground dumps shop location and ownership that can be accessed through any Tor-.

The Darknet Drugs
Dec aggravated in part by a big theft, fully shutdown by 23 December. Hyperboria "binds people together in a network that severs the link between them and their IP addresses" (Hodson, 2014, p. Its products are classed into various subcategories, ranging from Weeds, Hash, Concentrates, Edibles, etc. For example, it seems inevitable that insider information will become available on the darknet. Already, markets like Evolution will have taken the clients and sellers from Silk Road 2. This year saw law enforcement agencies effectively shutting down some of the biggest sites on the market including Alphabay and Hansa. Ellie also the onion directory worked at Cisco in Corporate Development doing acquisitions, investments, and strategy within the unified communications, enterprise software, mobile, and video sectors. The Extended Boolean Information Retrieval (EBIR) uses generalized distance functions to determine the similarity between weighted Boolean queries and weighted document vectors; see further Salton, Gerard, Fox, Edward A.